Custom Android Automotive OS launcher for TAG
A technical proof of concept (PoC) for a restricted, policy-driven in-car infotainment system
TAG
Services
PoC development
Technology
Android Automotive OS, Google Cloud Console, Figma
Validating a secure Android Automotive OS modification
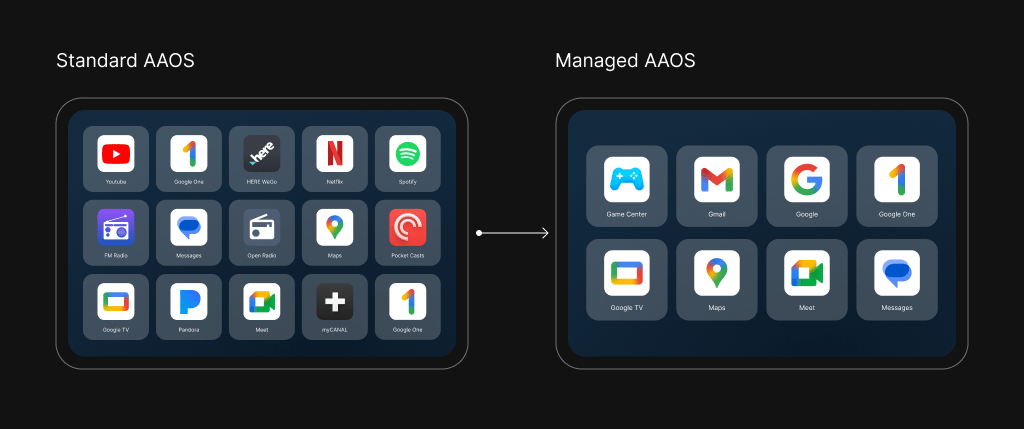
TAG, a US-based company that serves the Orthodox Jewish community, required a technical feasibility study. The company needed to know if a custom launcher could replace the standard interface on an Android Automotive OS (AAOS) head unit. In this particular case, the goal was to block access to specific applications and enforce network-level content filtering via DNS and proxy settings.
TAG selected Bamboo Apps to build this proof of concept. The client’s internal team would handle the backend, and Bamboo Apps was tasked to build the user-facing launcher and test the device policy controls.
Building a functional PoC and uncovering platform barriers
Bamboo Apps initiated the project with a focused plan to validate the core requirements. We started configuring device policies and app restrictions through the Google Cloud Console using the client’s own account.
However, during the Proof of Concept (PoC) phase, our team discovered a critical platform limitation. We quickly identified that it was not possible to develop a custom solution for managing devices due to Google’s verification requirements. Google does not allow random applications to use Mobile Device Management (MDM) capabilities directly – only apps verified as MDM providers can access these functions. Hence, the application cannot be registered as an MDM without going through this verification process with Google. This meant that deploying a custom launcher as the default system UI on Android Automotive would require integration with a certified MDM system.
Testing the boundaries of AAOS device management
The central technical challenge proved to be bureaucratic rather than architectural. Android Automotive OS reserves system-level controls, such as setting default launchers and enforcing global DNS, for applications that hold MDM privileges. Google issues these privileges only to companies that complete a formal verification process. TAG did not have this status.
Working on the PoC helped us answer a significant ‘unknown’ about AAOS or MDM restrictions – specifically, how the MDM setup is working for cars. This process was not clearly described anywhere. For phones and tablets, MDM typically requires app installation or setup during the initial start, but neither of these approaches is feasible for cars.

Clarifying the hypothesis for our client
The PoC allowed TAG to test its hypothesis with minimal investment. Within two weeks, the client confirmed the technical feasibility of the launcher itself but also learned of the insurmountable MDM barrier. This clarity prevented TAG from committing to a full-scale development project that would have failed during production. As a result, the company used the findings to reassess its product strategy.
For Bamboo Apps, the project added valuable internal knowledge about AAOS enterprise limitations.